
A cyber attack can strike when you least expect it. When it does, every second counts. Circular IT group’s Cyber Incident Response offers fast, flexible and secure IT replacement to get your business back on track.
Request a quote
A cyber attack can strike when you least expect it. When it does, every second counts. Circular IT group’s Cyber Incident Response offers fast, flexible and secure IT replacement to get your business back on track.
Request a quoteUnlike a planned IT migration, a cyber incident comes without warning. Systems crash, data is locked or lost, and your organisation grinds to a halt. Our response service provides fully configured servers, storage and networking equipment within hours.
This allows you to restore operations quickly, protect your data and limit the overall impact. Whether the cause is ransomware, phishing or human error, we are ready to step in when it matters most.
Request a quote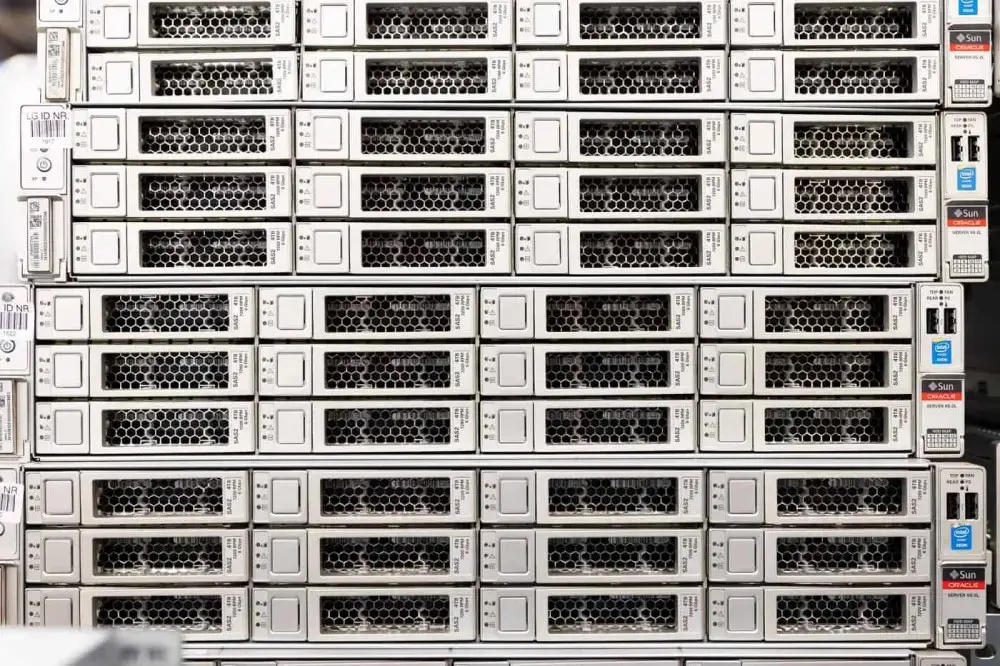

What is data destruction and why is it important?
Understanding how data is permanently removed, and why that matters, is essential in a world where information security plays a central role.

RAM Shortage 2026: What It Means for Enterprise IT Infrastructure
Global demand for RAM is rising rapidly as AI and cloud computing drive unprecedented pressure on memory supply. Discover what is causing the RAM shortage and how it affects enterprise IT infrastructure and hardware procurement.

How Can DaaS Simplify Joiners & Leavers?
A Device as a Service (DaaS) model helps organisations handle these transitions smoothly, efficiently, and without unnecessary cost.
A cyber incident is any unauthorised or unintended event within an IT system, network or application. This can range from a minor virus infection to a complex cyber attack that puts sensitive data or business operations at risk.
Phishing emails, malware, ransomware, unpatched software, weak passwords, human error and software vulnerabilities are the most frequent triggers for cyber incidents.
The impact can be severe: financial loss, reputational damage, exposure of confidential data, business disruption and potential legal or regulatory consequences.
We can deliver replacement IT infrastructure within hours, depending on the urgency and scope of your needs.
We supply ready-to-deploy servers, storage systems, network hardware and appliances tailored to your environment.
Data security starts with a solid foundation: encryption, multi-factor authentication, up-to-date antivirus protection, and strong internal awareness. Equally important is keeping all equipment and software up to date with the latest versions and security patches.
Continuing to work with outdated or unsupported systems carries risks. For example, Windows 10 no longer receives updates after the end of support, leaving data exposed to potential threats.

Sander Cornelissens
We are happy to help you!
"*" indicates required fields